RELATED:
A Tasmanian technology expert says online users are ill-informed about what to do in the event of an online data breach and need to protect themselves from online crime.
Subscribe now for unlimited access.
$0/
(min cost $0)
or signup to continue reading
As names, birth dates, bank and credit card details, social security numbers, medical data and other personal facts are provided across internet platforms, the opportunity to steal this data increases.
As a result, changes to the law have occurred.
Before February 2018 organisations collecting data were under no obligation to report data breaches, but this changed when Australia introduced its Notifiable Data Breaches scheme.
University of Tasmania technology lecturer Joel Scanlan explained that small businesses and large organisations must now report a data breach to the Office of Information Commissioner within 30 days.
He said medical data breaches must be reported regardless of the size of the operation, but size thresholds existed for small business.
“A dental practice has to report the loss no matter what, but if a small business - like a guy mowing your lawns who has your credit card number, address and phone number - gets hacked, he doesn’t have to report,” Mr Scanlon said.
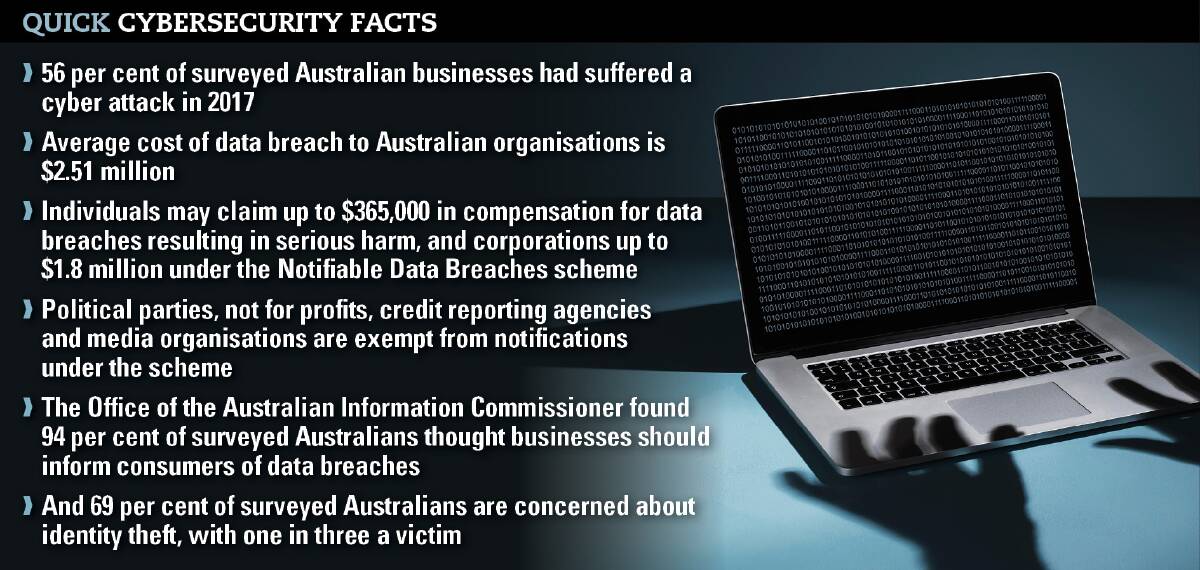
In the first six weeks of the scheme, 63 breaches were reported, which compared to 114 voluntarily reported breaches across the entire year of 2017.
“Organisations were just not telling people because it is bad press [for example] it may affect their stock price. Now if they don’t report there are very stiff penalties,” Mr Scanlon said.
While the scheme is welcome, there are questions about whether it goes far enough.
Europe introduced its General Data Protection Regulation in May this year, enforcing a 72-hour notification rule compared to Australia’s 30 days.
Further, the regulation also allows consumers to control their data.
“Things like your date of birth, age and address, that data is ours and we perceive that we own that information … but if someone is recording that information then they, in some way, own and control that data,” Mr Scanlan said.
“Currently this information can be recorded by companies without us even knowing about it.”
Mr Scanlan said a key part of regulation was the right to be forgotten, where consumers can tell organisations to delete all and any personal data.

Australian organisations and online businesses can currently store credit card and other personal details, but now in Europe, consumers can tell companies to delete it.
“That is where things are going globally, and hopefully Australia will go in that direction in the future,” he said.
Mr Scanlan added that multinational companies in Australia were already following the regulation.
“If a European citizen’s data is involved in an Australian data breach then they [the citizen] are covered by the [General Data Protection Regulation]… in the Australian context an awful lot of people would be covered,” he said.
“The fines are really substantial, proportional to the size of the company up to a percent of the net income. Google is currently being sued for $8 billion because of breaches.”
HOW TO PROTECT AGAINST DIGITAL THREATS
Mr Scanlan said education about what to do in the event of a breach was important.
If a breach has occurred and a password is stolen, and that same password or a variation is used for other applications, people should take action to change it.
They should also think what else is stored, such as bank details, and then ring banks to cancel cards.
“There are basic good habits that can end up protecting a person from the effect of a breach,” he said.
“If you use a password in more than one place then it is no longer private. Those who hack might try and use that password, with an email address that was also stolen, at 20 different websites.”
He said there were easy ways to find out which websites an email address had been previously used at, and simple ways to break passwords.
“A password with a number at the end does not present much of a problem to break,” he said.
“Things like your date of birth, age and address, that data is ours and we perceive that we own that information … but if someone is recording that information then they, in some way, own and control that data."
- UTAS technology lecturer Joel Scanlon
“This is where things like password managers come in handy, where passwords are never typed in or are randomly generated.”
Mr Scanlan said fingerprint, facial and iris biometric technology, being introduced by Samsung and Apple, were aimed at finding alternatives to passwords.
“It is about trying to find something that is more user friendly, which offers data security,” he said.
“Some people might not want a big company having their fingerprint or iris scan, and that is certainly a valid concern, but the biometrics are becoming particularly common … it is already happening at a government level.”
Mr Scanlan said the more information a person has about you, the easier it is to hack.
In relation to the recent Page Up data breach, which compromised Tasmanian data held by the state government and University of Tasmania, Mr Scanlan said names, phone numbers, birth dates, educational backgrounds, passwords and email accounts become a starting point to commit identity theft.
“They can move sideways into bank accounts and email accounts, and if you combine that information with looking at social media, then they might be able to find the answers to some of those security questions that the bank asks.”

